
FTX's Financial Collapse: A Study Using the Ishikawa Diagram
An analysis of the FTX collapse using the Ishikawa diagram, focusing on leadership failures and governance.
Read moreSecurity research, vulnerability analysis, and technical write-ups

An analysis of the FTX collapse using the Ishikawa diagram, focusing on leadership failures and governance.
Read more
A deep dive into the 'Use-After-Free' vulnerability in Chromium's CSS engine that allows for arbitrary code execution, now being actively exploited in the wild. Learn how a simple font stylesheet can lead to a full system takeover.
Read more
Want to learn Linux without abandoning Windows? Set up an isolated Linux VM using VMware Workstation Pro or VirtualBox — a must-have for cybersecurity, DevOps, and cloud beginners.
Read more
Deep dive into the critical Next.js middleware vulnerability that allows attackers to bypass authorization checks. Includes exploitation walkthrough and mitigation strategies.
Read more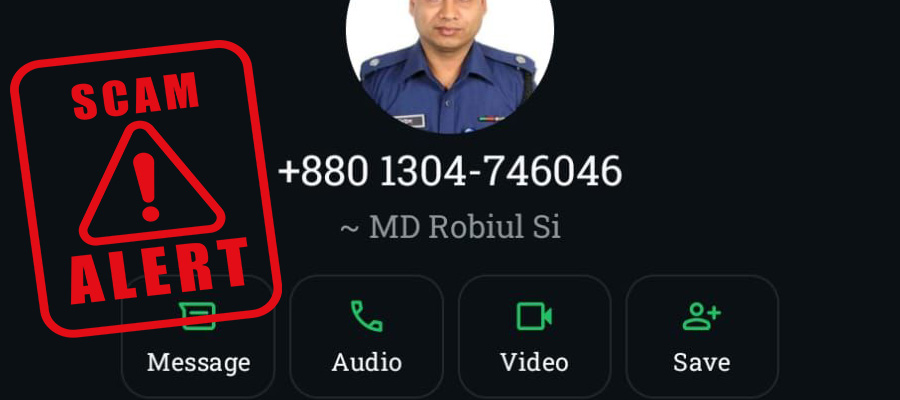
A real-life encounter with a WhatsApp scammer pretending to be a police officer. Learn how social engineering attacks work and practical tips to protect yourself from fake police scams.
Read more